| Welcome to The Cybersecurity 202! There are lots of mediocre-to-poor Christmas movies, but few truly good ones. "Scrooged" is on the good list, including the best film performance by David Johansen. Programming note: We're publishing through Thursday, then taking a break until the new year. Below: Huawei appears to have played a larger role in Chinese state surveillance than previously acknowledged, and cybersecurity pros are scrambling to patch one of the most widespread Internet vulnerabilities in years. | The Postal Service created a mobile voting system rife with security pitfalls | 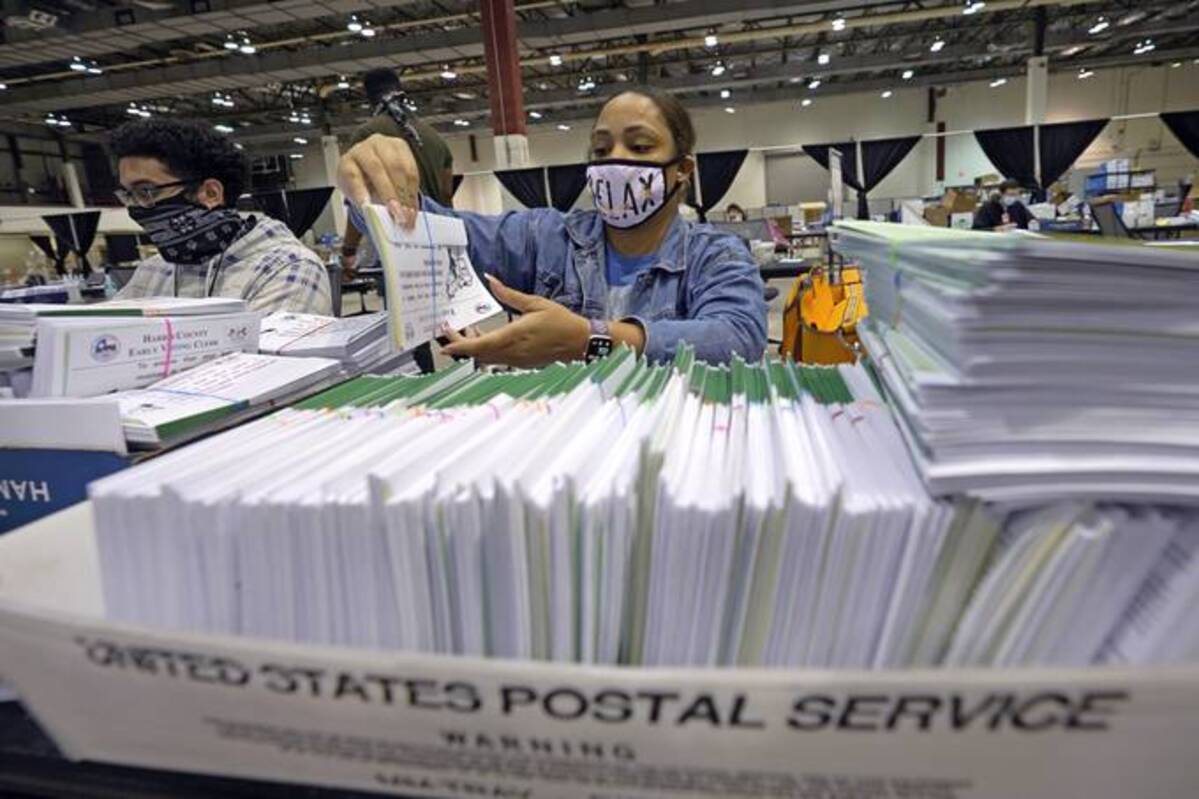 An election worker prepares mail-in ballots for the 2020 election. (David J. Phillip/AP) | | | In a previously undisclosed mobile voting project, the U.S. Postal Service was experimenting with risky voting technology before 2020, even as other parts of the government were scrambling to make voting more secure. The Postal Service built and secretly tested the blockchain-based system at the University of Colorado at Colorado Springs in 2019, apparently without help from parts of the government more closely focused on election security, as I reported with Jacob Bogage. The testing didn't go well. During a mock election on campus, university cybersecurity researchers were able to impersonate voters, attack the blockchain system so votes couldn't be trusted and flood the system with information so it became too overwhelmed to function. They used other techniques that undermined voters' privacy and the secrecy of the ballot. "Based on our research, this actually causes more problems than it solves," Shawn M. Emery, one of the researchers and a cybersecurity PhD candidate at the university, told me. "If three researchers can do this much damage, I can't imagine what a nation state actor with millions of dollars in its budget could do in order to break this election system in multiple ways." The Postal Service abandoned the project well before the 2020 election, spokesman David Partenheimer said. | | Yet USPS's secrecy is galling election security officials and advocates. They say it could fuel conspiracy theories and degrade public faith in the democratic process. Those concerns have been supersized since the 2020 election, bolstered by baseless claims of election fraud by former president Donald Trump and his supporters. "If you're doing anything in the election space, transparency should be priority number one. There should be no guessing game around this," Matt Masterson, a former senior adviser to the Cybersecurity and Infrastructure Security Agency, told me. | | @mastersonmv | "If you're doing anything in the election space, transparency should be priority number one. There should be no guessing game around this." | | | | | | | | Masterson was the government's chief liaison to state and local election officials before 2020. He said he was never aware of the Postal Service's plan while he was in office. CISA declined to comment. | - The Postal Service was awarded a public patent for the concept in August 2020 but had not previously revealed that it built a prototype system or tested it.
- The Colorado researchers were made to sign a nondisclosure agreement that prevented them from identifying the organization that built the prototype. In an academic paper describing the testing, they said it was built by "a U.S. government organization, that has requested to remain unnamed [and] plays an important role in national elections."
| | Partenheimer defended the research: "Blockchain technology's potential to strengthen digital transaction security is a concept we have explored on our journey to better meet our customers' current and future needs, and to bridge the gap between the physical and digital worlds. But we don't have plans to advance this system," he said. The test results are yet another blow for mobile voting systems, which election officials have long warned are the voting method least secure against hacking. The big problem: | - There's no physical record of a mobile vote. That means there's no way for voters to verify their ballots were recorded accurately or for auditors to double-check them after the fact.
- It would also be far easier for hackers to infect voters' own phones or laptops with malicious software that alters such votes rather than to compromise election machines, which are supposed to be completely segregated from the public Internet.
| | "It's scandalous for a government entity to conduct research into the security of blockchain online voting, which shows how insecure it is, but then hide the results and deprive the public and officials of these findings for over two years," Susan Greenhalgh, senior adviser on election security for the group Free Speech For People, told me. | | CISA was warning against mobile and other paperless voting systems at the same time the Postal Service was testing its prototype. The agency published a May 2020 assessment with the FBI, the Election Assistance Commission and the National Institute of Standards and Technology warning that mobile voting systems carried high risks to the "confidentiality, integrity, and availability of voted ballots." Despite security concerns, there has been a concerted push to expand mobile voting in recent years — spurred by the hope of making voting more convenient and accessible. West Virginia, Delaware and New Jersey have all allowed some voters to cast ballots using mobile apps in recent years. The programs were limited to voters with disabilities that made in-person or mail voting difficult and, in some cases, to overseas voters. Reviews of the apps used in those states conducted by the Massachusetts Institute of Technology turned up numerous cybersecurity problems. | | |  | The keys | | A major bug in widely used software is already being weaponized by government-backed hackers | | CISA Director Jen Easterly called the Log4j software bug "one of the most serious I've seen in my entire career, if not the most serious," CyberScoop's Tim Starks reports. Cybersecurity researchers have warned it could take months or years to mitigate damage from the vulnerability. China-linked hackers have already begun exploiting the bug, cybersecurity firm Mandiant told The Cybersecurity 202. "This will be everyone's problem soon," said John Hultquist, Mandiant vice president of intelligence analysis. Other cybersecurity firms, such as Sophos and Check Point, say they haven't seen ransomware groups or advanced hacking groups use it — yet. The big problem: The Log4j software that contains the bug is used by a broad range of industries — from major tech companies to the popular Minecraft video game. Developers use the software to log errors and other software events. The flaw is in an outdated version of the open-source tool, but one that many users haven't updated. | Chinese tech giant Huawei pitched its technologies for surveillance |  The new information comes amid growing concerns in China and around the world about facial recognition, biometric tracking and surveillance. (Andrea Verdelli/Bloomberg) | | | More than 100 marketing presentations reviewed by The Washington Post "show Huawei pitching how its technologies can help government authorities identify individuals by voice, monitor individuals of political interest, manage ideological reeducation and labor schedules for prisoners, and help retailers track shoppers using facial recognition," Eva Dou writes. Some of the slides were marked "confidential." The presentations were on a public-facing Huawei website before the company removed them last year. Customers not clear: "The Post could not confirm whom the Chinese-language presentations were shown to, or when. Some of the slides showcase surveillance functions specific to police or government agencies, suggesting that Chinese government authorities may have been the intended audience," Eva writes. Many of the PowerPoints appear to have been created in 2013 and 2014. Huawei denied any connection to the slides. The company has "no knowledge of the projects mentioned in The Washington Post report," the company said. China's embassy said criticism of the company was groundless. Eva rounds up five of the most relevant surveillance slides here. They relate to: | - Voice recording analysis
- Detention center monitoring
- Location tracking of political individuals of interest
- Police surveillance in the Xinjiang region
- Corporate tracking of employees and customers
| NSO Group has held talks on shutting down its Pegasus spyware division or selling the company |  The U.S. government last month blocked NSO from receiving U.S. technologies. (Sebastian Scheiner/AP) | | | Two U.S. investment funds have discussed taking control of NSO and shuttering Pegasus, Bloomberg's Yaacov Benmeleh and Eliza Ronalds-Hannon report. If that were to take place, the funds would invest around $200 million to turn the spyware firm into a defensive cybersecurity company. An NSO spokeswoman declined to comment to Bloomberg. Pegasus is a moneymaker for NSO, bringing in around half of its revenue. But it's also highly controversial. It has been used to target journalists, human rights activists and business executives, an investigation by The Washington Post and 16 media partners found. The U.S. government blacklisted the firm last month, blocking it from receiving U.S. technology, after the Biden administration found that it was used to "maliciously target" academics, activists, government officials and journalists. | | |  | Government scan | | Ransomware takes Virginia's legislature offline |  The cyberattack came in the busiest time of the year for Virginia lawmakers. (Steve Helber/AP) | | | Hackers appear to have launched the attack Friday, but it only came to the attention of most legislators and staffers Monday, Laura Vozzella and Gregory S. Schneider report, citing a legislative staffer. The hack has frozen legislators and staff out of the system they use to request, draft and modify bills at the busiest time of the legislative year, the staffer said. "You can't do anything with legislation right now," they said. "It will likely not be a quick fix." | CISA's advisory committee met for the first time | | The committee discussed boosting the country's cybersecurity and countering disinformation, the Hill's Maggie Miller reports. The committee chose Southern Company CEO Thomas Fanning as its chair and Mastercard Chief Security Officer Ron Green as vice chair. The committee also set up subcommittees focused on: | - Developing the cyber workforce
- Boosting all organizations' cybersecurity
- Developing a Technical Advisory Council made up of security researchers
- Combating misinformation and disinformation
- Strengthening critical infrastructure organizations' cybersecurity in the wake of cyberattacks
| | |  | Global cyberspace | | | |  | Cyber insecurity | | | |  | Daybook | | - The McCain Institute for International Leadership hosts an event on how NATO can combat misinformation and disinformation today at 1 p.m.
- Silverado Policy Accelerator chairman Dmitri Alperovitch discusses cybersecurity threats at an event hosted by cybersecurity venture capital firm NightDragon on Tuesday at 2:30 p.m.
- Sen. Angus King (I-Maine) speaks at an Atlantic Council event on maritime cybersecurity on Tuesday at 3 p.m.
- The Institute for Security and Technology hosts an event on U.S. Cyber Command's options to combat ransomware on Wednesday at 3 p.m.
- Former Cybersecurity and Infrastructure Security Agency director Chris Krebs discusses the relationship between technology and democracy at a Washington Post Live event on Thursday at 9:30 a.m.
- Homeland Security Secretary Alejandro Mayorkas, European Commissioner for Home Affairs Ylva Johansson, Europol Executive Director Catherine De Bolle and U.S. Secret Service Assistant Director Jeremy Sheridan discuss ransomware at a German Marshall Fund event Thursday at 2:30 p.m.
| | |  | Secure log off | | | Thanks for reading. See you tomorrow. | | |